Thread-Safe Initialization of Data
The story is simple if the data is not modified when shared between threads. The data has only to be initialized in the thread-safe way. It is not necessary to use an expensive lock for each access.
There are three ways in C++ to initialize variables in a thread-safe way.
- Constant expressions
- The function std::call_once, in combination with the flag std::once_flag
- Static variables with block scope
Constant expressions
Constant expressions are expressions that the compiler can initialize during compile time. So, they are implicit thread-safe. Using the keyword constexpr in front of the expression type makes it a constant expression.
constexpr double pi=3.14;
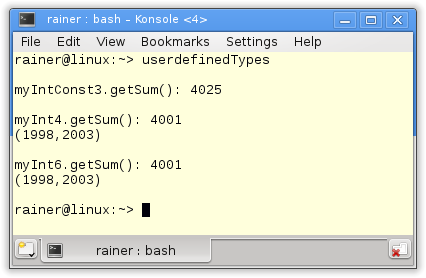
In addition, user-defined types can also be constant expressions. There are a few restrictions for those types to initialize them at compile time.
- They must not have virtual methods or a virtual base class.
- Their constructor must be empty, and itself be a constant expression.
- Their methods, which can be callable at compile time, must be constant expressions.
My struct MyDouble satisfies all these requirements. So it’s possible to instantiate objects of MyDouble at compile time. This instantiation is thread-safe.
struct MyDouble{ constexpr MyDouble(double v): val(v){} constexpr double getValue(){ return val; } private: double val; }; constexpr MyDouble myDouble(10.5); std::cout << myDouble.getValue() << std::endl;
The function call_once, in combination with the once_flag
By using the std::call_once function, you can register all callables. The std::once_flag ensures that only one registered function will be invoked. So, you can register more different functions via the once_flag. Only one function is called.
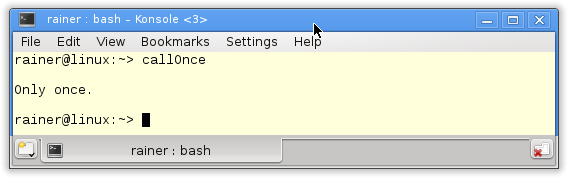
The short example shows the application of std::call_once and std::once_flag.
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 |
// callOnce.cpp #include <iostream> #include <thread> #include <mutex> std::once_flag onceFlag; void do_once(){ std::call_once(onceFlag, [](){ std::cout << "Only once." << std::endl; }); } int main(){ std::cout << std::endl; std::thread t1(do_once); std::thread t2(do_once); std::thread t3(do_once); std::thread t4(do_once); t1.join(); t2.join(); t3.join(); t4.join(); std::cout << std::endl; } |
The program starts in four threads (lines 17 – 20). Each of them should invoke the function do_once. The expected result is that the string “only once” is displayed only once.
 Modernes C++ Mentoring
Modernes C++ Mentoring
Do you want to stay informed: Subscribe.
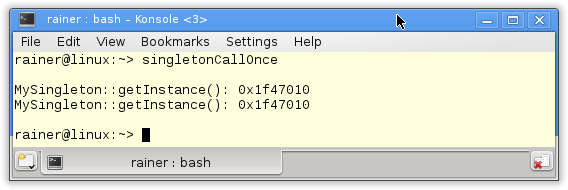
The famous singleton pattern guarantees only one instance of an object will be created. That is a challenging task in a multithreaded environment. But, thanks to std:.call_once and std:once_flag the job is a piece of cake. Now the singleton is initialized in a thread-safe way.
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 |
// singletonCallOnce.cpp #include <iostream> #include <mutex> class MySingleton{ private: static std::once_flag initInstanceFlag; static MySingleton* instance; MySingleton()= default; ~MySingleton()= default; public: MySingleton(const MySingleton&)= delete; MySingleton& operator=(const MySingleton&)= delete; static MySingleton* getInstance(){ std::call_once(initInstanceFlag,MySingleton::initSingleton); return instance; } static void initSingleton(){ instance= new MySingleton(); } }; MySingleton* MySingleton::instance= nullptr; std::once_flag MySingleton::initInstanceFlag; int main(){ std::cout << std::endl; std::cout << "MySingleton::getInstance(): "<< MySingleton::getInstance() << std::endl; std::cout << "MySingleton::getInstance(): "<< MySingleton::getInstance() << std::endl; std::cout << std::endl; } |
At first, the static std::once_flag. This is in line 9, declared and initialized in line 29. The static method getInstance (lines 28 – 21) uses the flag to ensure that the static method initSingleton (lines 23 – 25) is executed exactly once. In the body of the method, the singleton is created.
The output of the program is not so thrilling. The MySingleton::getIstance() method displays the address of the singleton.
The static story goes on.
Static variables with block scope
Static variables with block scope will be created precisely once. This characteristic is the base of the so-called Meyers Singleton, named after Scott Meyers. This is by far the most elegant implementation of the singleton pattern.
#include <thread> class MySingleton{ public: static MySingleton& getInstance(){ static MySingleton instance; return instance; } private: MySingleton(); ~MySingleton(); MySingleton(const MySingleton&)= delete; MySingleton& operator=(const MySingleton&)= delete; }; MySingleton::MySingleton()= default; MySingleton::~MySingleton()= default; int main(){ MySingleton::getInstance(); }
Using the keyword default, you can request special methods from the compiler. They are special because only a compiler can create them. With delete, the result is that the automatically generated methods (constructor, for example) from the compiler will not be created and, therefore, can not be called. If you try to use them, you’ll get a compile-time error. What’s the point of the Meyers Singleton in multithreading programs? The Meyers Singleton is thread-safe.
A side note: Double-checked locking pattern
Wrong beliefs exist, that a double-checking locking pattern is an additional way for the thread-safe initialization of a singleton in a multithreading environment. The double-checked locking pattern is – in general – an unsafe way to initialize a singleton. It assumes guarantees in the classical implementation, which the Java, C#, or C++ memory model don’t give. The assumption is that the access of the singleton is atomic.
But what is the double-checked locking pattern? The first idea to implement the singleton pattern in a thread-safe way is to protect the initialization of the singleton by a lock.
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 |
mutex myMutex; class MySingleton{ public: static MySingleton& getInstance(){ lock_guard<mutex> myLock(myMutex); if( !instance ) instance= new MySingleton(); return *instance; } private: MySingleton(); ~MySingleton(); MySingleton(const MySingleton&)= delete; MySingleton& operator=(const MySingleton&)= delete; static MySingleton* instance; }; MySingleton::MySingleton()= default; MySingleton::~MySingleton()= default; MySingleton* MySingleton::instance= nullptr; |
Any issues? Yes and no. The implementation is thread-safe. But there is a significant performance penalty. An expansive lock protects each singleton access in line 6. That also applies to reading access. Most time, it’s not necessary. Here comes the double-checked locking pattern to our rescue.
1 2 3 4 5 6 7 |
static MySingleton& getInstance(){ if ( !instance ){ lock_guard<mutex> myLock(myMutex); if( !instance ) instance= new MySingleton(); } |
I use an inexpensive pointer comparison in line 2 instead of an expensive lock a. Only if I get a null pointer I apply the expensive lock on the singleton (line 3). Because there is the possibility that another thread will initialize the singleton between the pointer comparison (line 2) and the lock (line 3), I have to perform an additional pointer comparison on line 4. So the name is clear. Two times a check and one time a lock.
Smart? Yes. Is thread safe? No.
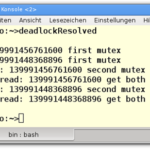
What is the problem? The call instance= new MySingleton() in line 4 consists of at least three steps.
- Allocate memory for MySingleton
- Create the MySingleton object in the memory
- Let instance refer to the MySingleton object
The problem: there is no guarantee about the sequence of these steps. For example, for optimization reasons, the processor can reorder the steps to the sequences 1,3, and 2. So, in the first step, the memory will be allocated; in the second step, the instance refers to an incomplete singleton. If, at that time, another thread tries to access the singleton, it compares the pointer and gets the answer true. So, the other thread has the illusion that it’s dealing with a complete singleton.
The consequence is simple: program behavior is undefined.
What’s next?
At first, I should continue in the next post with the singleton pattern. But to write about the singleton pattern, you should have a basic knowledge of the memory model. So I continue in the sequence of my German blog. The next post will be about-thread local storage. If we are done with the high-end API of multithreading in C++, I’ll go further with the low-end API. (Proofreader Alexey Elymanov)
Thanks a lot to my Patreon Supporters: Matt Braun, Roman Postanciuc, Tobias Zindl, G Prvulovic, Reinhold Dröge, Abernitzke, Frank Grimm, Sakib, Broeserl, António Pina, Sergey Agafyin, Андрей Бурмистров, Jake, GS, Lawton Shoemake, Jozo Leko, John Breland, Venkat Nandam, Jose Francisco, Douglas Tinkham, Kuchlong Kuchlong, Robert Blanch, Truels Wissneth, Mario Luoni, Friedrich Huber, lennonli, Pramod Tikare Muralidhara, Peter Ware, Daniel Hufschläger, Alessandro Pezzato, Bob Perry, Satish Vangipuram, Andi Ireland, Richard Ohnemus, Michael Dunsky, Leo Goodstadt, John Wiederhirn, Yacob Cohen-Arazi, Florian Tischler, Robin Furness, Michael Young, Holger Detering, Bernd Mühlhaus, Stephen Kelley, Kyle Dean, Tusar Palauri, Juan Dent, George Liao, Daniel Ceperley, Jon T Hess, Stephen Totten, Wolfgang Fütterer, Matthias Grün, Phillip Diekmann, Ben Atakora, Ann Shatoff, Rob North, Bhavith C Achar, Marco Parri Empoli, Philipp Lenk, Charles-Jianye Chen, Keith Jeffery, Matt Godbolt, Honey Sukesan, bruce_lee_wayne, Silviu Ardelean, schnapper79, Seeker, and Sundareswaran Senthilvel.
Thanks, in particular, to Jon Hess, Lakshman, Christian Wittenhorst, Sherhy Pyton, Dendi Suhubdy, Sudhakar Belagurusamy, Richard Sargeant, Rusty Fleming, John Nebel, Mipko, Alicja Kaminska, Slavko Radman, and David Poole.
| My special thanks to Embarcadero |  |
| My special thanks to PVS-Studio |  |
| My special thanks to Tipi.build |  |
| My special thanks to Take Up Code |  |
| My special thanks to SHAVEDYAKS |  |
Modernes C++ GmbH
Modernes C++ Mentoring (English)
Rainer Grimm
Yalovastraße 20
72108 Rottenburg
Mail: schulung@ModernesCpp.de
Mentoring: www.ModernesCpp.org


Leave a Reply
Want to join the discussion?Feel free to contribute!